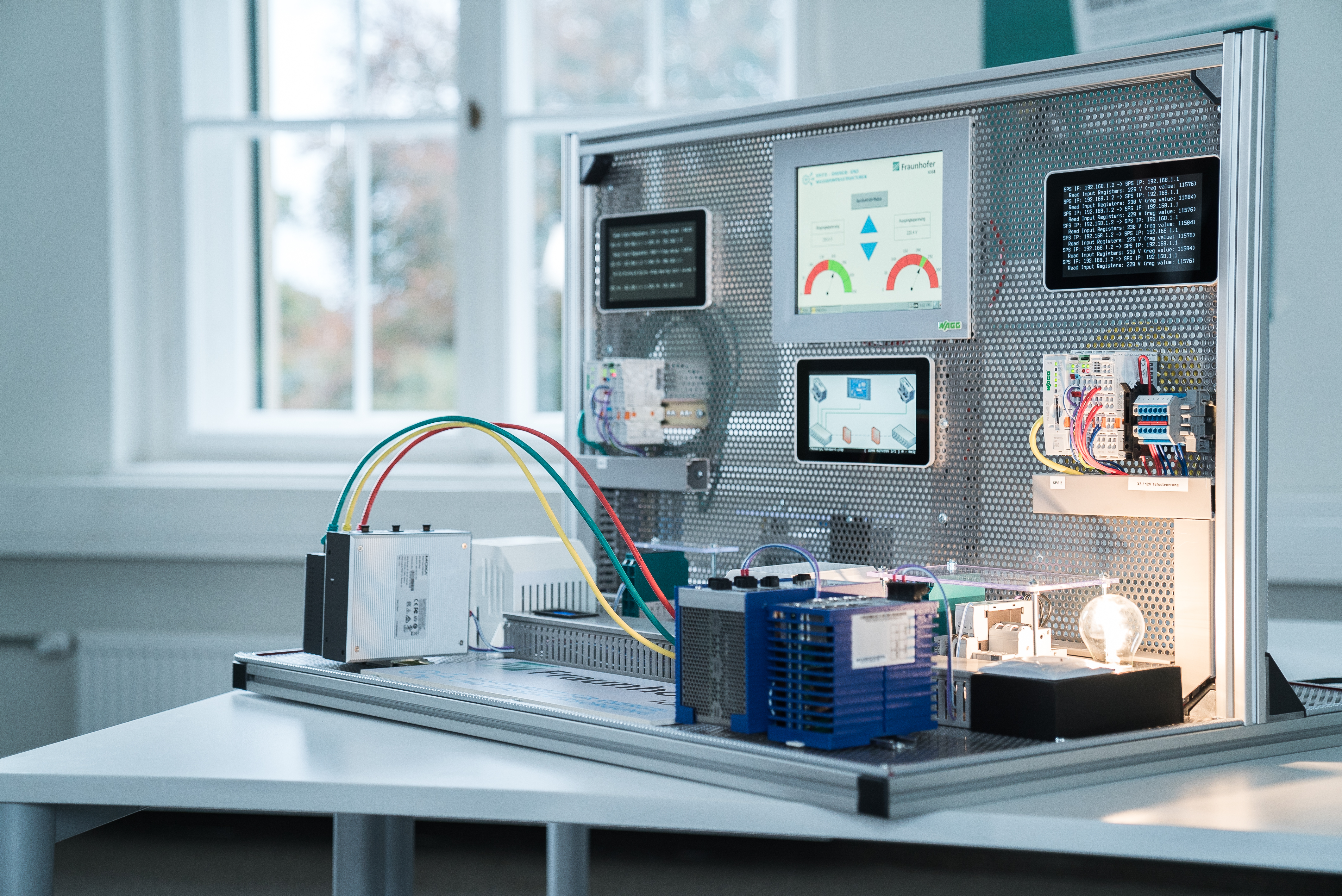
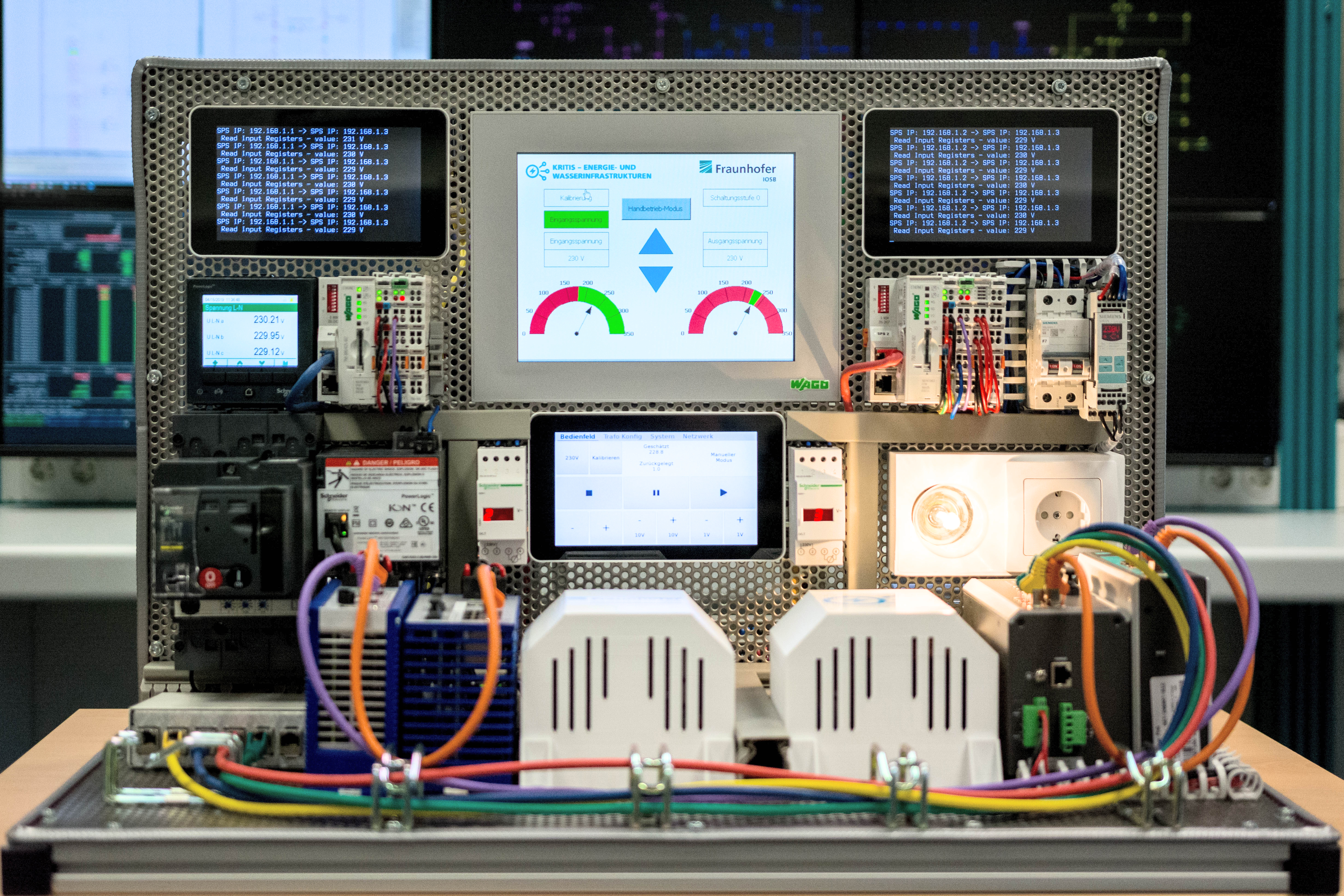
The mobile demonstrator is used as an exercise platform in the courses of the Cybersecurity Energy and Water Supply Learning Lab in order to deepen the taught training content in practice by the participants.
A real process from the field level of energy supply serves as a use case, for which various attack scenarios on the IT and OT infrastructure have been designed. The training participants learn about different attack patterns, their impact on the overall system and how to defend against attacks by properly using IT security tools and building additional barriers against intrusions into the IT infrastructure. The tools range from basic techniques such as proper setup of network components to monitoring and analysis of IT and OT network traffic and hardening of automation systems.
The communication system includes two firewalls as well as switches from different manufacturers, so that the participants are taught different ways of implementing the individual measures and can more easily transfer what they have learned to their own system landscape.
The training participants are given the opportunity to work on the topics very close to the hardware and not only by means of virtual environments or simulations. The aim of the training is to defend against various attack patterns and to secure the power supply in the demonstrated scenario.
Attack patterns
- Man-in-the-middle
- DDoS attacks
- Physical access
- Bruteforce and dictionary attacks
- Protocols:
- IEC 60870-5-104
- IEC 61850
- Modbus u.a.
Defensive measures
- Secure configuration of network components
- Hardening of control systems
- Network monitoring
- Intrusion detection, intrusion prevention
Use cases
- Attack vectors on remote control components and communication infrastructure
- Communication disruption
- Manipulation of sensor data, status information
 Advanced System Technology branch AST of Fraunhofer IOSB
Advanced System Technology branch AST of Fraunhofer IOSB